© 2026 NervNow™. All rights reserved.
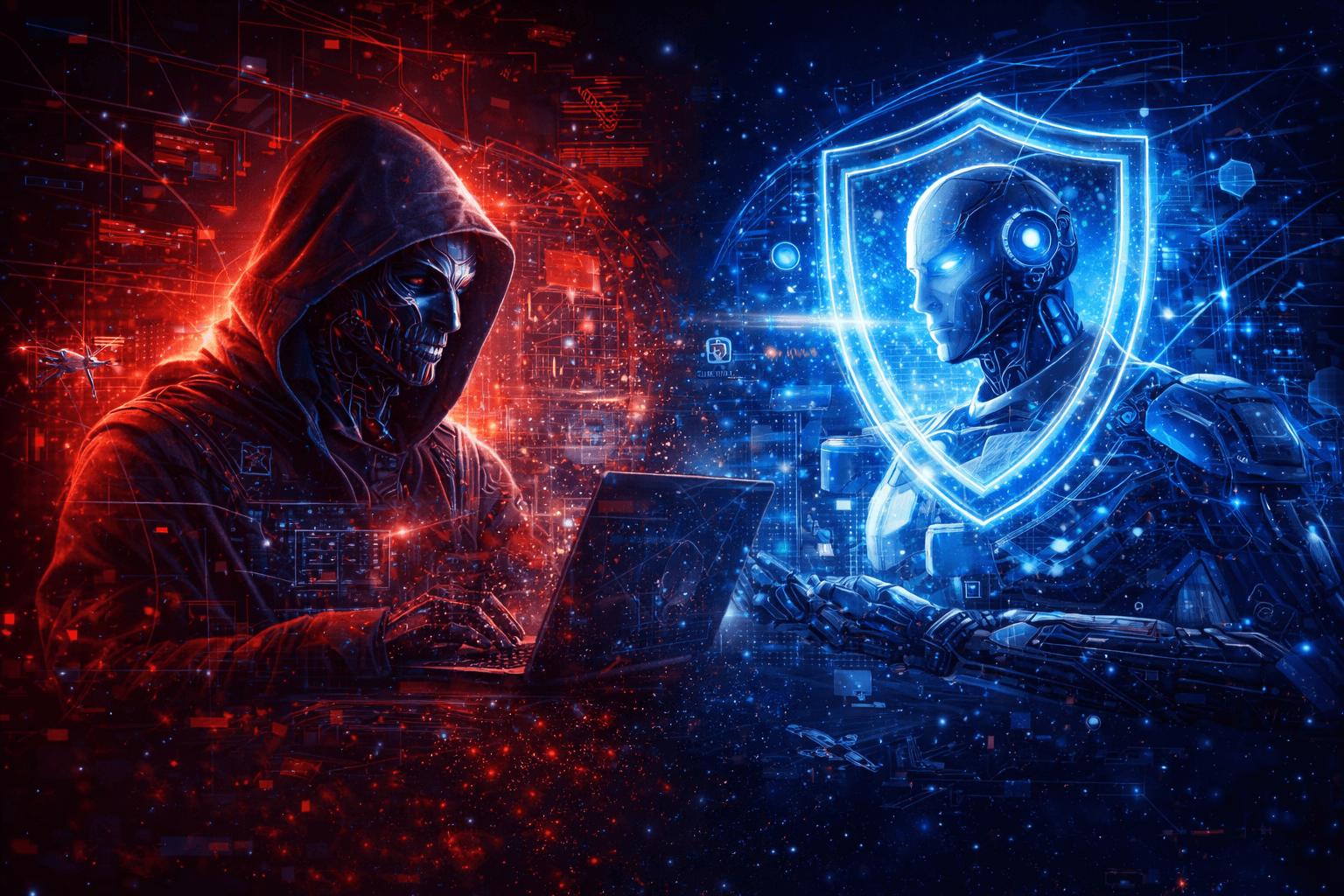
AI is Cybersecurity’s Deadliest Weapon and Strongest Shield
Artificial Intelligence is transforming cybersecurity faster than any prior technological shift. While AI accelerates innovation, productivity, and automation, it simultaneously enables cyber adversaries to launch faster, more scalable, and more sophisticated attacks. This article presents a strategic executive-level analysis of the AI–cyber paradox: AI as both a weapon and a shield. It outlines current threat realities, organizational blind spots, and practical actions leaders must take within the next 90 days to remain resilient in an AI-native threat landscape.
The Wake-Up Call
In January 2024, a finance executive at Arup, a global engineering firm, joined a video call with the company’s Chief Financial Officer and several senior colleagues to discuss a confidential transaction. The conversation was detailed and professional. The faces were familiar. The voices were accurate. After thorough discussion, the executive authorised 15 wire transfers totalling $25 million. Weeks later came the devastating discovery: every person on that call, except the victim, was an AI-generated deepfake. No system was hacked. No firewall was breached. Artificial intelligence impersonated the leadership team so convincingly that an experienced professional could not tell the difference.
Generative AI, the fastest-adopted technology in human history, reaching 100 million users in just two months has handed cybercriminals capabilities that were once the exclusive domain of nation-state intelligence agencies. Here is the paradox every executive leader must now confront: the same AI technology driving your innovation agenda is simultaneously the weapon being used against you, and the most powerful shield available to defend your organization.
The AI–Cyber Paradox: Acceleration on Both Sides of the Battlefield
Artificial Intelligence is not simply introducing new cybersecurity threats. It is compressing time across the entire threat landscape. Attack preparation cycles that once took weeks can now be executed in hours. Attack campaigns that required large criminal teams can now be automated by individuals using AI-assisted tooling. Simultaneously, defensive capabilities are improving at similar velocity, creating a dynamic technological arms race.
On the offensive side, generative AI enables attackers to craft highly personalized phishing campaigns using publicly available data, generate realistic deepfake audio and video capable of bypassing traditional identity verification processes, and automate vulnerability discovery across massive codebases. AI systems can simulate attack pathways, test exploit scenarios, and refine attack strategies continuously.
On the defensive side, AI is transforming detection, response, and predictive security intelligence. Modern AI security platforms can analyze millions of telemetry signals in real time, detect anomalous behavior patterns invisible to human analysts, and automatically initiate containment actions. Generative AI is also being deployed inside security operations to summarize incidents, generate investigation reports, and accelerate analyst decision cycles.
The underlying cybersecurity challenges have not fundamentally changed. The critical shift is velocity. Both attack and defense decision windows are shrinking toward real-time execution.
The Invisible Risk: Uncontrolled Organizational AI Adoption
One of the most underestimated risks in the AI era is internal, not external. Many organizations are expanding their cyber attack surface unintentionally through unmanaged AI adoption. Employees are increasingly using external AI tools for productivity, research, coding assistance, and content generation without enterprise security oversight. This phenomenon, often referred to as shadow AI, introduces unmonitored data exposure pathways that bypass traditional security controls.
The rapid experimentation with AI agents introduces a second layer of risk. Organizations are deploying semi-autonomous or autonomous systems capable of accessing enterprise data, executing business workflows, and interacting with external services. Without strong governance frameworks, these systems can create unintended data access patterns, compliance violations, or operational risks.
The core issue is governance lag. Technology adoption is moving faster than policy development, risk assessment processes, and regulatory interpretation. This mismatch is creating systemic exposure across industries.
The Strategic Evolution of Cybersecurity Leadership
Cybersecurity is no longer an IT support function. It is now a core business strategy discipline. Leading organizations are integrating cybersecurity leadership directly into enterprise transformation initiatives, cloud modernization programs, and AI deployment strategies.
The role of the Chief Information Security Officer is evolving from technical risk manager to enterprise business risk strategist. CISOs are increasingly participating in board-level technology investment discussions, regulatory risk interpretation, and digital transformation planning. Organizations that treat cybersecurity as a compliance exercise rather than a strategic capability are creating long-term competitive disadvantage.
Cyber maturity is now directly correlated with business resilience, brand trust, and operational continuity.
The Operational Reality: Why AI Defense Is No Longer Optional
Traditional human-driven security operations centers cannot scale to the volume, complexity, and speed of modern cyber threats. Security alert volumes alone have exceeded human processing capacity in most large enterprises. AI-augmented security operations are rapidly becoming the baseline rather than an advanced capability.
Modern defensive architectures are incorporating AI-driven anomaly detection, automated incident response orchestration, continuous adversarial simulation, and predictive threat intelligence. The shift is moving from reactive incident management toward anticipatory risk prevention.
Organizations that fail to adopt AI-assisted defense capabilities will face increasing asymmetry against adversaries who are already using AI to accelerate attack operations.
Immediate Strategic Actions for Executive Leadership
Organizations that are successfully navigating the AI–cyber transition share several behavioral patterns. They lead with business risk problems rather than technology experimentation. They prioritize speed of risk visibility over perfection of risk controls. They embed security into AI initiatives at design stage rather than adding controls after deployment.
In the immediate term, organizations must establish full visibility into AI usage across the enterprise. This includes sanctioned platforms, unsanctioned employee tools, embedded vendor AI functionality, and experimental deployments across business units. Without visibility, meaningful risk management is impossible.
Board-level governance must also evolve. AI risk should be treated as enterprise risk rather than technology risk. Leadership teams must define risk tolerance thresholds for AI deployments, establish governance tracking mechanisms, and maintain active awareness of organization-specific AI threat exposure.
Technology investment strategy must also shift toward targeted AI-enabled cybersecurity use cases. High-return implementations such as phishing detection, vulnerability prioritization, and automated alert summarization provide immediate defensive value without requiring enterprise-wide transformation.
Existing enterprise risk frameworks do not need replacement, but they require extension. Modern frameworks must account for prompt injection, model poisoning, adversarial machine learning manipulation, and AI-enabled data exfiltration risks. Effective risk models evaluate exposure across four core layers: data, models, applications, and infrastructure.
Finally, organizations must recognize that AI is also the most realistic solution to the cybersecurity talent shortage. AI copilots, automated compliance systems, and simulation-based training environments can significantly multiply the effectiveness of existing security teams.
The Future State: AI-Native Cyber Resilience
The convergence of AI and cybersecurity represents a structural shift in competitive positioning. Organizations that successfully integrate security into AI innovation cycles will be able to move faster, deploy more confidently, and scale digital operations more safely.
Organizations that separate AI innovation from cybersecurity governance will experience increasing exposure to systemic cyber risk and operational disruption.
The defining leadership decision is no longer whether AI will reshape cybersecurity posture. That transformation is already underway. The strategic decision is whether organizations will guide that transformation deliberately or react to it after risk events occur.
Conclusion
Artificial Intelligence is neither inherently a cybersecurity threat nor inherently a security solution. It is a force multiplier operating across both domains simultaneously. Organizations that understand and operationalize this duality will define the next era of digital trust, enterprise resilience, and secure innovation.
The strategic window for proactive transformation remains open, but it is narrowing rapidly.
References (APA Style)
CrowdStrike. (2024). Global IT outage incident analysis report.
Deloitte. (2024). Global future of cyber survey.
Deloitte. (2026). Tech trends 2026: AI and cyber convergence.
Interpol. (2025). Global cybercrime threat assessment.
World Economic Forum. (2025). AI governance and cyber risk framework.
Disclaimer: The author is a contributor to NervNow and a cybersecurity professional working with Deloitte. All views expressed are personal and do not represent the official positions of Deloitte, NervNow, or any affiliated organizations.